
All Bitcoiners keep repeating that Bitcoin is a true monetary revolution. I am in the same case since I keep repeating it over and over again. We cannot do otherwise, since it is obvious from our point of view.
If Bitcoin’s domination is based on its superior monetary attributes, it is its technology that gives credibility to these attributes.
The Bitcoin protocol is indeed what allows tens of millions of users to have absolute confidence in Bitcoin. In September 2020, Bitcoin passed the 100 million user mark. In February 2021, Bitcoin surpassed the $1 trillion market cap for the first time.
All this would not have been possible without the genius of Satoshi Nakamoto in designing the Bitcoin system.
However, contrary to what some people believe, the magic of the Bitcoin protocol is due to the assembly of different technological elements already proven. If you take the time to read the Bitcoin white paper, you will see that the key elements that are at the heart of the system have been known for a long time.
The Bitcoin protocol is based on private/public keys and Merkle trees
The private/public keys used at the heart of the Bitcoin protocol are based on the Elliptic Curve Digital Signature Algorithm (ECDSA). More specifically, Bitcoin uses a special curve called secp256k1.
This curve has an order of 256 bits, taking 256 bits as input, and returning an integer of 256 bits as output.
To represent the transaction data of a block, the Bitcoin protocol relies on a particular data structure called Merkle Tree. This is a tree in which each leaf node is labeled with a block of data, and each non-leaf node is labeled with a cryptographic hash of the labels of its child nodes:
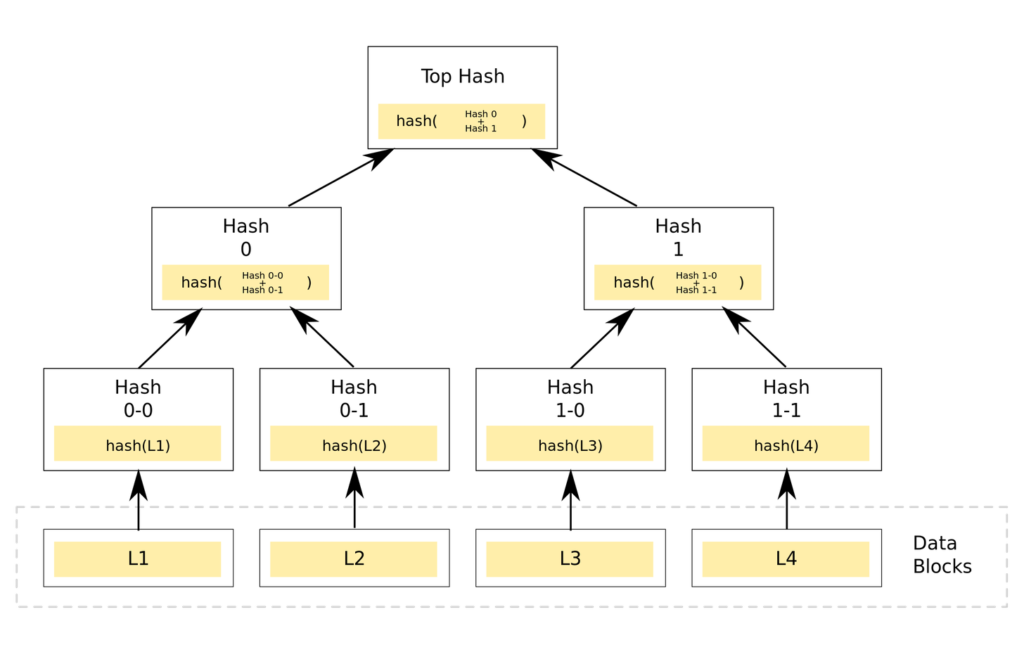
The purpose here is to ensure that data blocks received by other nodes in the Bitcoin network are received without damage or alteration. It is even possible to verify that other nodes are not lying by trying to send false data blocks.
Cryptographic hash functions are used ingeniously in the Bitcoin protocol
For the cryptographic hash function, Satoshi Nakamoto has relied on the SHA-256 algorithm, also known for a long time.
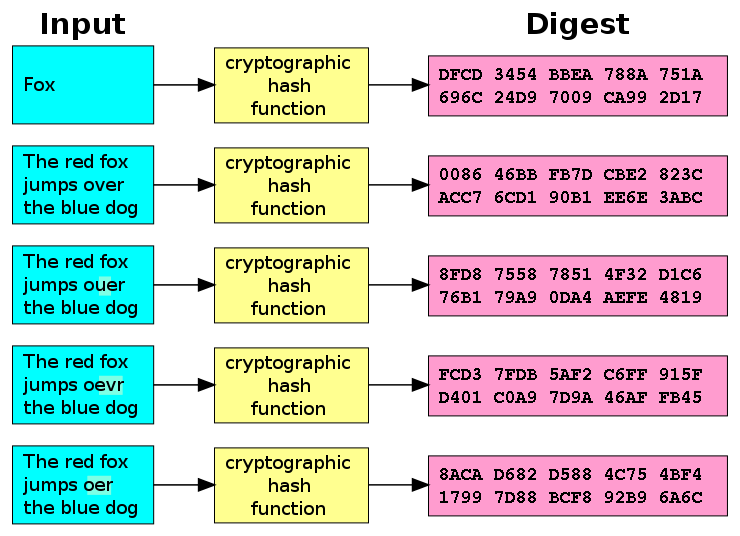
A cryptographic hash function will take data as an input and produce an output of fixed length. This output is usually represented by a string of characters in hexadecimal format.
These functions are deterministic, which means that if you input the same string of characters several times for a given function, you will get the same output each time. The following illustration gives a good visual overview of what a cryptographic hash function is:
More importantly, a cryptographic hash function has the distinct advantage of being a one-way function. It can therefore be easily computed but very difficult to reverse. These functions are often referred to as “trapdoor functions”:
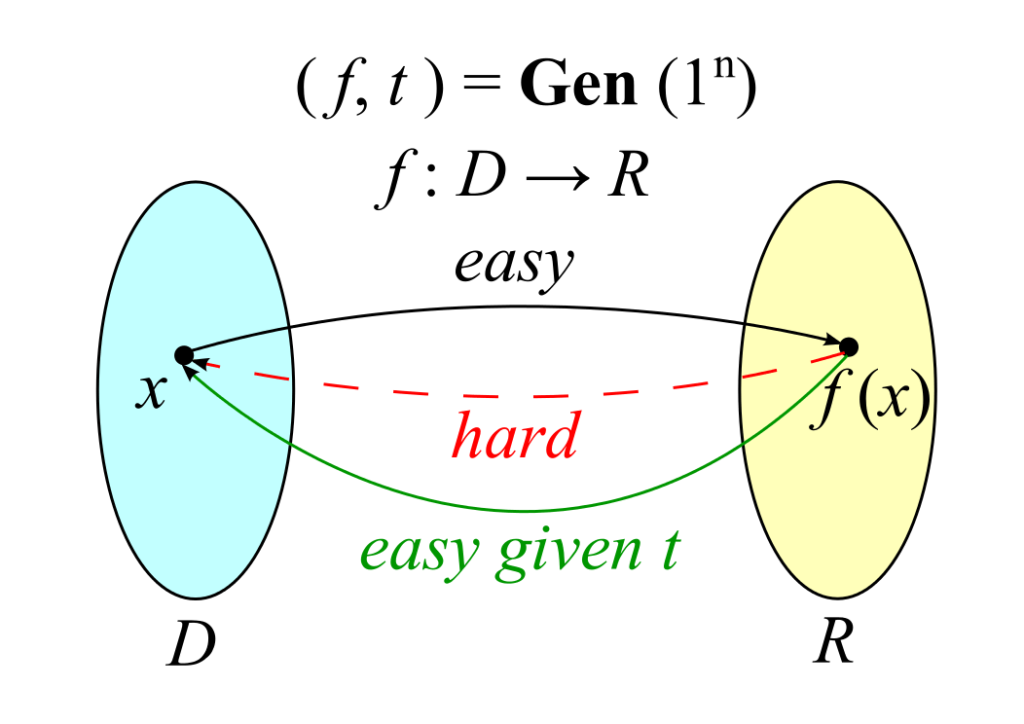
While calculating the hash of a string with a cryptographic hash function is very fast, the reverse calculation is very complex and time-consuming.
Indeed, there is nothing more efficient than a stupid and mean systematic approach during which it will be necessary to test all possible combinations at the input of the hash function to find the same output.
The Proof-Of-Work algorithm uses the properties of the cryptographic hash functions
The Proof-Of-Work algorithm relies on cryptographic hash functions to work.
Given a certain difficulty, the Bitcoin network miner must find a hash for the block starting with a given number of zeros. As shown in the previous diagram, the miner has the result of f(x) starting with a certain number of zeros.
He then has to find the value x that allows him to reach this result. To do this, at each attempt, he increments by one an integer variable called nonce within the block being mined.
The more the difficulty increases, the more difficult it becomes. The greater the miners’ computing power, the more possible values they can test per second. They maximize their chance of finding the right x value, and thus of getting the Bitcoin reward for correctly adding a new block to the Bitcoin Blockchain.
The mining difficulty is automatically adjusted every 2,016 mined blocks
This is where Satoshi Nakamoto thought of everything.
He planned an automatic difficulty adjustment to mine new blocks every 2,016 mined blocks. This corresponds to an adjustment every two weeks since on average 144 blocks are mined every day. This adjustment keeps the predictability of new BTC issuance over time.
As the Hash Rate available on the Bitcoin network increases, the difficulty increases in relation to the next adjustment. When the Hash Rate drops, the difficulty is adjusted downwards.
To give you an idea, here is the evolution of the difficulty on the Bitcoin network for mining a block:
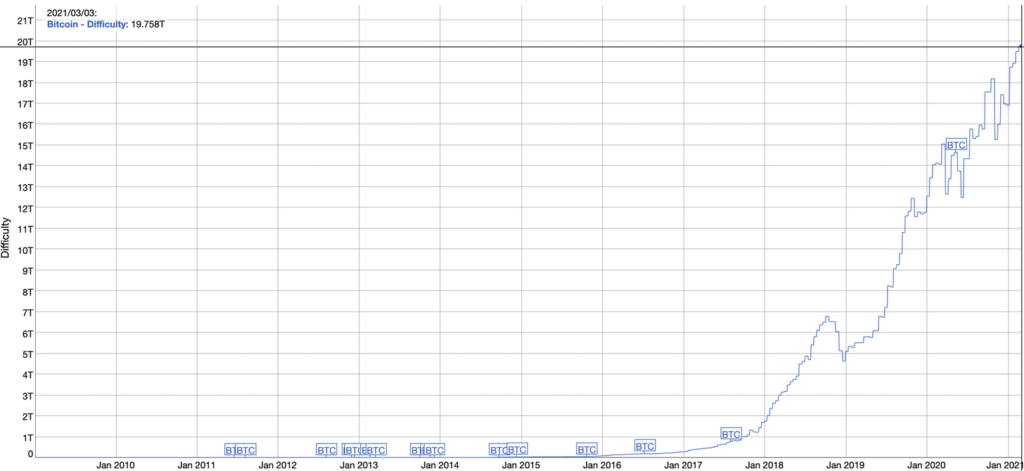
As you can see, this difficulty continues to increase over time. Bitcoin network is therefore a little more secure every day than it was the day before.
The reward for miners is divided by two for every 210,000 blocks mined and tends towards zero over time
Another key technological element of the Bitcoin protocol is the automatic halving of the Bitcoin reward every 210,000 mined blocks. This gives Bitcoin a quantitative hardening type of monetary policy.
The last Halving took place in May 2020. At each Halving, a supply shock occurs in the Bitcoin world. The supply of newly issued Bitcoins is halved, while the maximum supply remains fixed at 21 million units. Together with a constantly increasing demand for Bitcoin, this produces a significant increase in the price of Bitcoin.
Another important element that I haven’t mentioned so far is the timestamping of the Bitcoin Blockchain blocks.
Each block contains a date in Unix format. This is part of the hash of a block and makes it more difficult to manipulate the Bitcoin Blockchain. Indeed, a timestamp is considered valid only if it is larger than the median timestamp of the previous 11 blocks and smaller than the adjusted network time + 2 hours.
“Network-adjusted time” is the median of the timestamps returned by all nodes connected to your node. As a result block timestamps are not exactly accurate, and they do not need to be. Block times are accurate only to within an hour or two.
The final touch is the networking of the Bitcoin system in P2P mode
Finally, all this is networked via a P2P architecture. Bitcoin is a completely decentralized network. Its Blockchain is permissionless and trustless. This means that anyone can become a node in the Bitcoin network. This is something I urge you to do to really take control of your money.
By putting your savings into the Bitcoin network, you become your own bank branch.
By running your own node on the Bitcoin network, you become a bank on your own. This is the highest level of sovereignty that everyone should aim for in the Bitcoin system.
Final Thoughts
As I have shown you, the magic of Bitcoin lies in the unique assembly of all those technological elements that existed before. However, no one had ever thought of combining them in this way.
This is where Satoshi Nakamoto’s genius lay.
It is thanks to this design that the Bitcoin system became the first successful implementation of a digital currency. If Bitcoin is a technological disruption in its own right, it is above all its implementation to give credibility to its monetary attributes that should be remembered here.
The next time you decide to put the fruits of your labor into the Bitcoin network, you will have a better understanding of why it is completely safe to use the Bitcoin protocol. For the rest, I advise you to go further by discovering the Ten Commandments of Bitcoin.
Wanting more insights on Bitcoin? Join In Bitcoin We Trust Newsletter.